Multifamily application fraud has become a persistent risk, and it’s only getting more challenging for operators. Survey data show that threats are rising, with operators reporting more frequent fraud attempts and greater financial consequences. What was once an occasional disruption is now a daily operational headache.
The evolution of applicant fraud is, like many things in the real estate industry, powered by artificial intelligence, which has dramatically lowered the barrier to entry. Tasks that once required time, technical skill, or coordination can now be executed faster and at scale, producing highly convincing application materials in minutes. The result is a constant cat-and-mouse game where operators deploy third-party detection tools, fraudsters adapt, and the gap between defense and offense continues to narrow.
This report explores how multifamily fraud is evolving, from the rise of synthetic identities to the growing vulnerabilities inside leasing workflows. It also examines how operators are responding, from layered verification strategies to the expanding ecosystem of fraud-detection vendors, and what it will take to build more resilient screening systems to defend against sophisticated fraud attempts.
Fraud is now a relentless risk
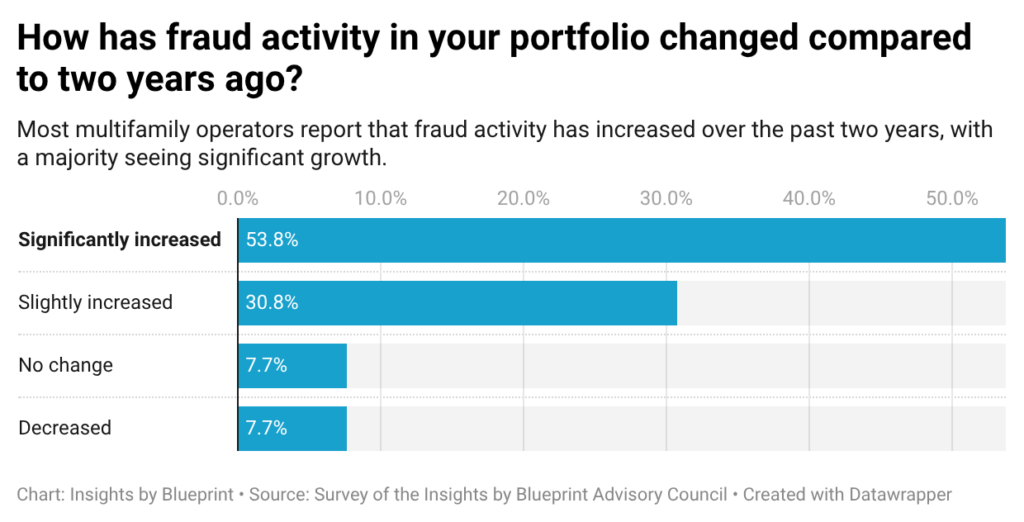
Our recent survey of the Insights by Blueprint Advisory Council reveals that multifamily application fraud is rising fast, becoming more sophisticated, and may be outpacing the industry’s ability to fully contain it. What was once an occasional issue is now relentless. Roughly 85% of respondents reported an increase in fraud activity, with more than half calling that increase significant. A minority of respondents saw no change or a decline, reinforcing that this is not a temporary spike but a sustained trend.
The financial impact is already meaningful. Nearly 70% of operators said fraud is having a moderate-to-severe effect on their portfolios, with 23% reporting severe losses. Not a single respondent reported zero impact. Even at a relatively small scale, fraud has moved beyond nuisance into a tangible financial risk in day-to-day operations.
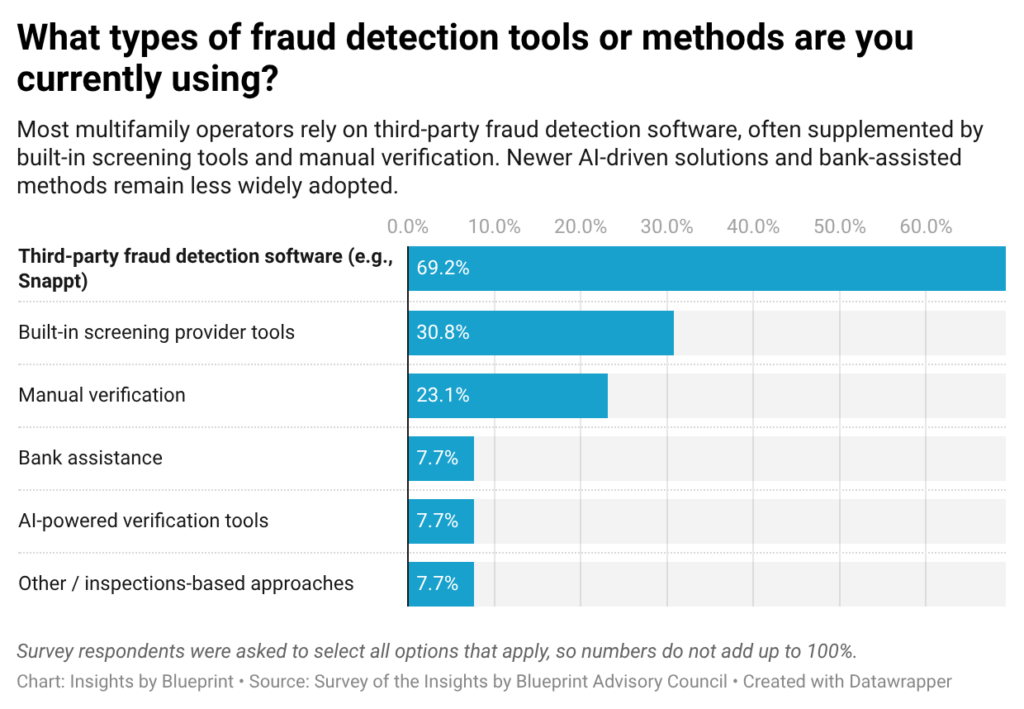
In response, the industry has largely standardized around third-party verification tools. About 69% of respondents rely on platforms such as Snappt, while smaller shares rely on built-in screening systems or manual processes. While existing tools are widely regarded as effective — 100% of respondents rated them at least moderately so — they may not be keeping pace with the evolving threat landscape.
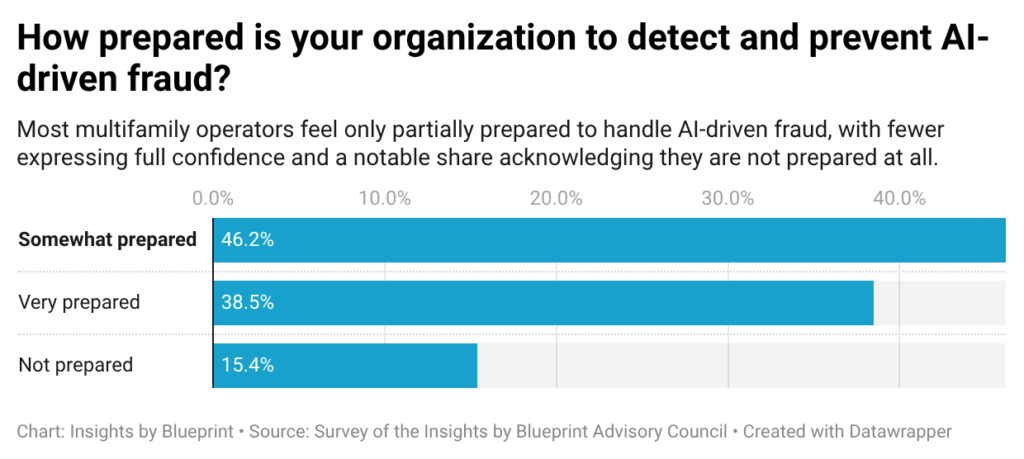
That gap is being driven by AI. More than three-quarters of respondents have already seen an increase in AI-generated fraud, often reporting a significant jump. Yet preparedness remains limited: only 38% feel very prepared to respond to AI-generated fraud, while the majority say they are only somewhat prepared or not prepared at all.
As a result, fraud strategy is shifting toward a layered approach. Operators are combining third-party tools with internal systems and manual verification, cross-checking data sources, validating document origins, and introducing human oversight at critical points. Fraud is now an ongoing, complex risk that requires integrated, multi-layered defenses.
The barrier to entry has collapsed
According to numerous sources we spoke with, multifamily application fraud is moving from crude document fabrication to much more sophisticated identity-based deception. The most serious emerging threats include stolen identities, synthetic identities assembled from partial real data, and AI-generated financial and employment documents that are internally consistent enough to survive first-pass review. Three factors appear to be changing at once:
First, the barrier to entry has collapsed. Several sources describe a world in which fraud no longer requires specialized criminal skill. Tools that once demanded Photoshop experience, manual editing, or a broader network can now be replaced by commodity AI products that generate professional-looking documents in minutes.
Second, fraud is becoming much harder to detect. In some cases, operators are not dealing with obviously fabricated identities, but with stolen real identities or synthetic ones built from authentic fragments of real information. That makes standard screening less effective because many systems are designed to detect inconsistencies rather than high-quality fakes built for internal coherence.
Third, the weakest link is often the workflow, not the tool. Handoffs, rushed reviews, shallow income checks, and overreliance on document uploads are the main points of failure. In other words, many operators are not losing to better fraud technology alone. They are losing to fraudsters who understand how leasing teams actually work.
Martin Orefice, CEO of Rent to Own Labs, said fake applicants, or real applicants with forged documents, have become an increasing problem for him at his rental properties. “One of the big challenges is the sheer number of versions of the same scam,” Orefice told us. Some people, he said, are standing up AI agents to drive up rents or test their evaluation system. Meanwhile, some individuals are using AI-generated bank statements and other documents to make their finances look better. “It’s gotten to the point where, along with multiple layers of documentation, I also need a face-to-face meeting with a potential tenant before moving forward,” he said.
Faster, cheaper, and repeatable
Artificial intelligence has changed the economics of fraud. Forged documents can now be generated quickly, cheaply, and repeatedly. Instead of one applicant taking a risk with a single poorly edited PDF, operators may now see multiple attempts built from templates that can be modified in seconds when challenged.
“Fraud that once required a network of people and weeks to prepare is now carried out by a single person in an afternoon,” said Tyler Rodgers, Founder and CEO of Privin Network, a global private investigation company operating in more than 50 countries. “AI tools can create a coherent identity package: photo ID, employment letter, bank statement, and rental reference that can go through visual inspection within hours, and there is enough internal consistency to convince a person they are real.”
Rodgers explained that cybercriminals in corporate screening have already learned to evade behavioral pattern checks on application timing, rotation, and varied document formatting to avoid red-flag anomalies. In multifamily, he said, the most exposed are the operators whose detection systems were configured to handle the volume and complexity of fraud three years ago.
Synthetic identity risk is growing
Synthetic identity fraud is especially dangerous because it can pass through systems designed to confirm that data points exist, rather than to verify that they belong together truthfully. A phone number may work, an employer may seem real, and a bank statement may look consistent. But the overall applicant may still be fictional. This is an important distinction for operators who assume fraud equals obvious forgery.
“Synthetic identity construction has become a leasing problem faster than most multifamily operators had envisioned,” said Rodgers. “These are not stolen identities. They are fake, constructed from bits of real data and backed by AI-generated pay stubs, fake rental records, and phone numbers that are successfully verified through carrier lookups.”
“We have yanked application packages in neighboring inquiries in which all single documentations seemed genuine, and a whole identity is never a reality,” Rodgers continued. “It is that disjuncture between the document’s appearance and its truth where screening is failing.”
Real identities are also being weaponized
Another worrying development: the use of real stolen identities with clean credit and legitimate rental histories. This is, in some ways, even more dangerous than synthetic identity fraud because standard systems may return clean results even when the underlying identity belongs to a real person with a genuine background. That creates a blind spot. Traditional tenant screening is often built to detect mismatches, gaps, or suspicious anomalies. But when the identity itself is real, the system may have very little reason to reject the applicant unless additional controls are in place.
Wendy Porter, CEO of New Home Atlanta, said that at the beginning of the application process, her team usually notices well-polished income documents. “Verification is very important, as they could be using fake identities to copy the profiles of real applicants,” she said. “Obviously, they do not look fake at first glance, as they are usually complete. This is why it really raises a concern on our end on how they can easily get past our initial check-up because, of course, nothing seems off right away.” Porter said that it is only later, during verification, when they take a closer look and realize that something is not as it seems.
Income verification is the weakest link
Income verification, according to Rodgers, is the weakest point in the fraud screening workflow. Rodgers said the majority of multifamily operators are verifying the authenticity of the documents. But few are questioning whether the employer or financial institution mentioned in the document can be independently validated as having a relationship with the applicant.
“The apparent loophole in that verification, which is the difference between document existence and document accuracy, is where organized fraud rings are focusing their efforts,” he said. “That is our standard practice of running that layer of verification in corporate due diligence. It is not often incorporated in the screening workflow in leasing operations.”
This is especially problematic in fast-moving leasing environments, where staff are under pressure to fill units and keep workflows moving. Speed can turn a shallow review into a feature, but fraudsters increasingly understand that. “Multifamily operators often become vulnerable because a detailed review is not prioritized, as they may focus mainly on finishing things fast,” Porter said. “In the Atlanta market, where applications move quickly, a minor oversight when checking documents can result in a mismatch in identity details, especially when the review process is too light or poorly connected.”
Workflow handoffs create hidden exposure
A document uploaded on one day may not be substantively reviewed until later. Identity checks, leasing software, and manual review may be handled as separate steps that do not fully integrate. That creates openings for fraud to slip through the cracks, especially when teams assume someone else in the workflow has already validated a key step. For operators, this is an important reminder that fraud prevention is not only about buying better detection software. It is also about understanding where process fragmentation is creating false confidence.
Operators are still optimized for yesterday’s fraud
Multifamily operators are still configured to catch the fraud they already know. Fraudsters, meanwhile, are adapting to those assumptions. They research screening practices, identify what gets checked and what gets skimmed, and build their strategies around those patterns. That creates a strategic mismatch. Operators often use controls designed for lower-volume, lower-complexity fraud. Bad actors are increasingly approaching leasing as a system to be tested.
Verifying the entire identity chain
There isn’t a single silver bullet for multifamily fraud prevention. What’s proving effective instead is a layered verification model that looks at the full picture rather than relying on any one check. That means cross-checking identity, income, and background together instead of reviewing each in isolation, and independently validating employers and financial institutions rather than trusting uploaded documents at face value.
It also requires maintaining human review at critical moments, especially when application packages appear unusually polished or internally perfect. In some cases, adding face-to-face, live video, or liveness-based checks can help confirm identity. Just as important is maintaining a healthy skepticism toward any document that cannot be traced back to a verifiable source, and tracking patterns over time rather than treating each application as a one-off event. Fraud prevention now requires operators to verify provenance, not just presentation. The question is no longer merely whether a document looks real. It is whether the data came from a trusted source and maps credibly to a live, verified person.
The fraud detection vendor landscape
The multifamily fraud detection landscape is anchored by a group of specialized vendors across key categories. In document fraud detection, Snappt is widely viewed as a leading provider, using AI to analyze pay stubs and bank statements. Celeri focuses on forensic document analysis. For income and employment verification, Argyle is gaining traction by connecting directly to payroll systems to verify income at the source, alongside VeriFast, which offers similar validation services.
Identity verification is increasingly handled by platforms like Persona, which provides ID checks and liveness detection, and Plaid, which provides access to bank accounts and financial data for verification. These tools are typically layered on top of traditional screening platforms such as TransUnion SmartMove, RentPrep, and First Advantage. Property management systems like RealPage and Entrata are also increasingly incorporating fraud-detection tools into leasing workflows.
Building a stronger, more robust defense
A fraudulent lease does not just create unpaid rent. It can trigger months of lost revenue, legal costs, turn expenses, staff time, and reputational strain. More importantly, it can distort how operators think about occupancy quality and collections performance. As fraud becomes more sophisticated, apparent leasing velocity may hide rising risk beneath the surface. That means fraud prevention belongs in broader conversations about revenue protection, bad debt management, staffing models, workflow design, and vendor selection. The operators most likely to adapt well are not necessarily the ones who treat every applicant as suspicious. They are the ones that redesign their leasing systems around a more realistic assumption: every uploaded document is untrusted until it can be tied back to a verifiable source.
– Nick Pipitone
Got tips or feedback? Email Nick at [email protected]





